NOTE: Reprinted with permission from the National Property Management Association. NPMA.org
Operation ID — developed by the police, but little known by the public — has very humble beginnings dating back to a time before mainframe computers and modern enterprise asset management systems. It goes back to a time when records were kept on index cards in tiny drawers, on sheets of paper in filing cabinets and in ledgers stored on bookshelves.
Mass Production Requires a New Police Response
In the early 1960s, the consumer electronics movement was in its infancy. Transistor radios were becoming popular and FM radio was just beginning to spread. In this period of mass production, identical items were assigned unique serial numbers for quality control purposes. If there was a problem with one item, it was likely the entire batch could be defective. Millions upon millions of identical consumer electronic items were flying off production lines and the only thing separating one from the other was a unique serial number. Those serial numbers provided an additional benefit in helping police solve crime.
The Simple and Elegant Operation ID Strategy
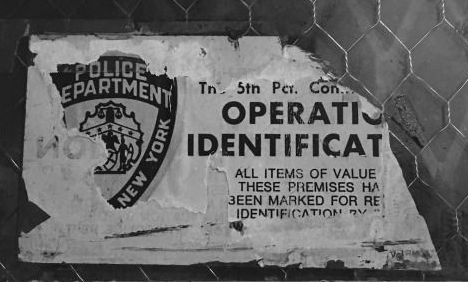
In response to the escalating numbers of burglaries and thefts of portable electronics, the Operation ID method was developed by law enforcement professionals in 1963 and rolled out nationally in 1979. The strategy was designed for individuals, families and small businesses. The strategy was simple then, and has changed little to this day:
- Mark property with a universal identifier
- Record serial numbers
- Post warning signs
By the time Operation ID was released in 1979 as a national response to property crimes, by the U.S. Department of Justice, 378 studies at a cost of $100 million (in 2018 money) had been conducted. Upon its release, Operation ID was endorsed by the International Association of Chiefs of Police, the National Sheriffs Association, the FBI and others. Many law enforcement agencies continue to stand by the strategy. The National Sheriffs Association still promotes the original strategy as does the NYPD.
- GGD-79-54 Department of Justice Should Explore the Feasibility of a Uniform Identification System for Marking Personal Property (gao.gov)
- Operation Identification | Neighborhood Watch Signs – National Neighborhood Watch Institute (NNWI)
- Services – Property Protection – NYPD (nyc.gov)
If citizens would just adopt the Operation ID strategy, the police would have a potent tool for solving property crimes. According to Wake Forest University Police:
Operation ID is a nationwide program designed to discourage burglary and theft of valuables. It also provides a way for you to easily identify stolen property, and increases law enforcement’s chances of recovery and conviction. Most burglars steal valuables for resale. But if you mark all items with permanent identification numbers, the burglar may be unable to sell them. If a criminal knows all your valuables are marked, he or she will look for easier and more profitable victims.
Operation ID Form – University Police (wfu.edu)
Serial Numbers Are the Key
According to Wikipedia, “Serial numbers are a deterrent against theft and counterfeit products, as they can be recorded; and stolen or otherwise irregular goods can be identified.” This is at the heart of why large institutions go to so much trouble to mark and register property — it’s a tragedy that so few individuals, homeowners and small businesses don’t mark theirs.
The Consumer Etching Tool
Mass produced etching/engraving tools — high-speed devices with high-strength steel or industrial diamond tips — were developed in the early ’60s. Etching tools can be used by consumers to easily mark items too hard to mark by hand. Police immediately saw a use for these etching tools and encouraged citizens to mark property with an identifier, so lost and stolen property could be easily identified and returned to the rightful owner. But the police worried about using a person’s name, address and phone number in case a stolen item would fall into the hands of violent criminals or other predators.
Finding a Universal Identifier
Recording serial numbers on a piece of paper and keeping them in a filing cabinet was simple enough, but Operation ID also requires that property be marked. In the 1960s, many states used Social Security numbers as driver’s license numbers. This was considered secure information as the internet had not yet been developed. So, the police recommended citizens etch their Social Security numbers into their personal belongings which only the police could access at the time. In later years, the universal identifier became a driver’s license number combined with the two-letter state abbreviation. Today, we look at both of these solutions as highly insecure.
Property Crimes Are Not Solved or Reported
Looking at the FBI’s 2010 Uniform Crime Reporting Program, when it comes to residential and small business burglaries and thefts, 90% of crimes are never solved. This is likely because citizens have not taken the critical step of recording serial numbers. The widespread use of alarms and security cameras has reduced burglaries and thefts only slightly. The police are really only interested in one thing: they want serial numbers to identify stolen items, but they’ve done a poor job of communicating this. The problem is that most people don’t have these records and don’t fully grasp why the police need them. The miniaturized enterprise asset management (mEAM) strategy is designed to make capturing the information the police need at the consumer level easy and online.
Miniaturized Enterprise Asset Management (mEAM)
Every large contractor, corporation, university, government and hospital knows the importance of having unique universal identifiers tied to its company name. For large institutions with EAM systems in place, there are policies and procedures for what to do in the event of a crime. The police typically want the make, model and serial numbers of stolen items, and it’s a snap for asset managers to access and deliver the pertinent information to law enforcement professionals very quickly, but not so with the general public.
With the advent of the internet, entrepreneurs began experimenting with ways to miniaturize enterprise asset management. In Europe there has been tremendous interest in figuring out ways to utilize the internet to create universal identifiers that are secure and globally accessible. There is so much interest that the Loss Prevention Certification Board issued two standards for the fledgling industry. One set of rules guiding database security and communication safety and the other setting out standards for asset marking systems.
- LPCB | Global Certification and Standards for Fire and Security (bregroup.com)
- LPS1224-3.1NCDraftDC.docx (redbooklive.com)
- LPS1225-3.2NCDraftDC.docx (redbooklive.com)
But according to consultant and retired police officer, Calvin Beckford, mEAM hasn’t caught on in Britain either.
Stolen Items Can Be Traced With Serial Numbers
Law enforcement professionals trace stolen property by entering the serial numbers into the FBI’s National Crime Information Center (NCIC) clearinghouse.
Today, this happens on laptops mounted right inside squad cars. Pawn shops check the massive NCIC for stolen property, and police recover huge caches of stolen property when they execute search warrants. Every serial number of recovered property is checked against the NCIC. When items are not listed in the NCIC, pawn shops can unknowingly resell stolen items and police warehouses fill up with untraceable items.
Who mEAM Helps
Very small businesses wanting to break into government contracting can do so with a mEAM system. This is a valuable opportunity for veteran-owned, women-owned and minority-owned small businesses looking for an edge in the government contracting arena. Also, large contractors often use subcontractors that could benefit from a smaller asset management strategy.
There are even a few instances where large enterprises don’t want to use their own asset tags to identify portable electronic items used in public, such as laptops, because it is a security risk. With a third-party mEAM system, the odds of recovery increase while not revealing the name of the rightful owner.
Today, third-party mEAM systems that use the underlying Operation ID approach have advanced the state of the art of the original strategy developed back in 1963. mEAM systems work by providing a low cost and reliable burglary deterrent and lost and found for individuals, homeowners and small businesses. This is because they get the same powerful tool large enterprises routinely have access to but in miniaturized form.
About the Author
Jon Shelness is from Des Moines, Iowa. He has a criminal justice and social work background, most recently having worked with court-ordered youth since 2003. In 2016, doing graduate research on neighborhood associations and Neighborhood Watch, he learned of the Operation ID strategy. Seeing an opportunity, he developed and launched a startup that advances the state of the art called My Property ID Registry.
About the Publisher
“The Origin and Evolution of Operation ID: A Strategy to Help Police Solve Crime” by Jon Shelness is reprinted with permission from the National Property Management Association. This article first appeared in the NPMA’s trade association publication, The Property Professional, in February 2019, volume 31, issue 1. NPMA is a non-profit membership association for professionals who are responsible for the effective and efficient management of equipment, materials, and other moveable and durable assets for their organization.